8-在公网服务器中搭建nginx反向代理
[toc]
概览
HomeLab中的服务逐渐增多,配置SSL的任务也繁琐起来,如果每次都是在对应docker内部部署证书过于麻烦,且无法统一自动化管理,所以改为在公网服务器搭建nginx反向代理,利用letsencrypt自动更新域名证书。
安装nginx
安装nginx
sudo apt install nginx启动nginx
sudo systemctl start nginx检查nginx状态
sudo systemctl status nginx安装后web目录:/var/www/html/
配置目录:/etc/nginx/
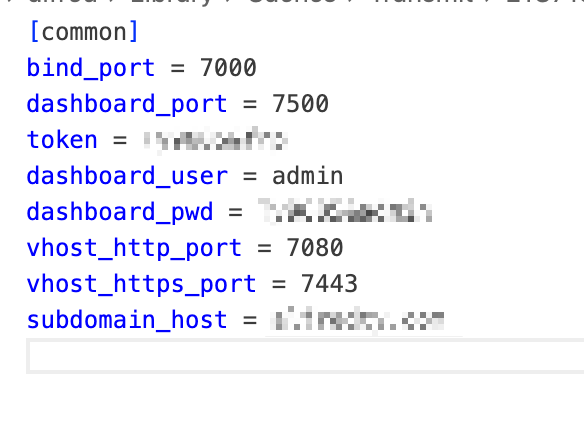
配置frp
因为要把80 和 443端口提供给nginx进行连接并反向处理,这里配置frp的vhost_http_port为7080,vhost_https_port为7443
配置nginx
无ssl配置
在nginx配置中增加一些server配置,此时80端口可以调通,基本就稳了,剩下的就是443的证书工作了
server {
listen 80;
# listen 443 ssl;
server_name alfredty.com;
client_max_body_size 1024M;
location / {
# proxy_pass http://alfredty.com:7080;
# proxy_set_header Host $host:$server_port;
proxy_pass http://alfredty.com:7080;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Host $host;
proxy_ssl_server_name on;
}
}
server {
listen 80;
# listen 443 ssl;
server_name tool.alfredty.com;
client_max_body_size 1024M;
location / {
# proxy_pass http://alfredty.com:7080;
# proxy_set_header Host $host:$server_port;
proxy_pass http://tool.alfredty.com:7080;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Host $host;
proxy_ssl_server_name on;
}
}
server {
listen 80;
# listen 443 ssl;
server_name op.alfredty.com;
client_max_body_size 1024M;
location / {
# proxy_pass http://alfredty.com:7080;
# proxy_set_header Host $host:$server_port;
proxy_pass http://op.alfredty.com:7080;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Host $host;
proxy_ssl_server_name on;
}
}
server {
listen 80;
# listen 443 ssl;
server_name git.alfredty.com;
client_max_body_size 1024M;
location / {
# proxy_pass http://git.alfredty.com:7080;
# proxy_set_header Host $host:$server_port;
proxy_pass http://git.alfredty.com:7080;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Host $host;
proxy_ssl_server_name on;
}
}
完成配置后重启nginx
service nginx restart配置证书
使用letsencrypt获得免费证书,通过其certbot获取和管理证书。
安装certbot
https://certbot.eff.org/instructions?ws=nginx&os=ubuntufocal&tab=standard
获取证书并修改nginx配置
获取证书:
# 先测试下(如果失败可能是nginx已配置了ssl证书,先注释下嘛)
sudo certbot certonly --nginx --dry-run
# 没问题再真的运行
sudo certbot certonly --nginx 
按照输出的证书路径配置nginx
server {
listen 80;
#请填写绑定证书的域名
server_name alfredty.com op.alfredty.com tool.alfredty.com git.alfredty.com;
#把http的域名请求转成https
return 301 https://$host$request_uri;
}
server {
#SSL 默认访问端口号为 443
listen 443 ssl;
#请填写绑定证书的域名
server_name alfredty.com;
#请填写证书文件的相对路径或绝对路径
ssl_certificate /etc/letsencrypt/live/alfredty.com/fullchain.pem;
#请填写私钥文件的相对路径或绝对路径
ssl_certificate_key /etc/letsencrypt/live/alfredty.com/privkey.pem;
ssl_session_timeout 5m;
#请按照以下套件配置,配置加密套件,写法遵循 openssl 标准。
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:ECDHE:ECDH:AES:HIGH:!NULL:!aNULL:!MD5:!ADH:!RC4;
#请按照以下协议配置
ssl_protocols TLSv1.2 TLSv1.3;
ssl_prefer_server_ciphers on;
location / {
proxy_pass http://alfredty.com:7080;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Host $host;
proxy_ssl_server_name on;
}
}
# ... 后面以此类推,只要配置op.alfredty.com tool.alfredty.com git.alfredty.com的443的server就可以了更新证书
# 测试更新
sudo certbot renew --dry-run
# 没问题再真的运行
sudo certbot renew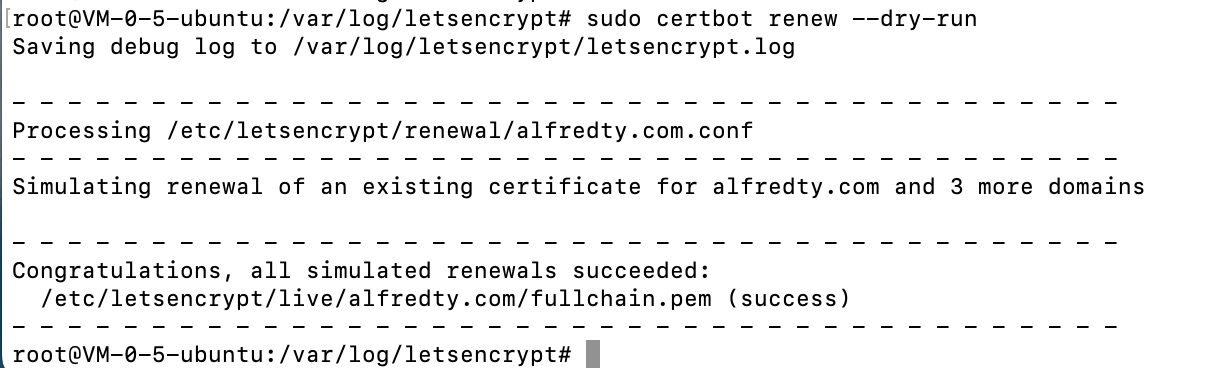
添加证书
后续如果有新的域名想要配置到证书中,可以直接用命令添加即可,记得要先把历史的也协商
certbot certonly --cert-name alfredty.com -d xxx.alfredty.com,yyy.alfredty.com,zzz.alfredty.com,alfredty.com,aaa.alfredty.com,bbb.alfredty.com,ccc.alfredty.com查看、管理证书
certbot certificates